A year of backdoors, exploits and pwning
I was very eager to join VIS’s hacking group flagbot (the CTF Committee). I had no inital experience with CTF and could barely read assembly code. After a few tutorial challenges, I was thrown into cold water as we participated in various online hacking competitions, including DEF CON qualifiers and an attack and defense CTF. What follows, are highlights of the past year from flagbot.
Baby Steps⌗
It all started with my first CTF meeting: I was eagerly wanting to learn “hacking stuff” and become the very best, when I was given my first CTF task: Baby ROP. I had no clue what “CTF” or “ROP” was, so Jonas (current CTF president) gave a small introduction to CTF: CTF - an abbreviation of Capture the Flag - is a sport which consists of solving computer science (hacking) challenges. A competition usually consists of many challenges and for every solved challenge you get a flag as proof of solving it. This flag can be redeemed for points, the team with the most points wins the competition. These challenges are grouped into five major categories: pwnables, reversing, web, crypto and misc.
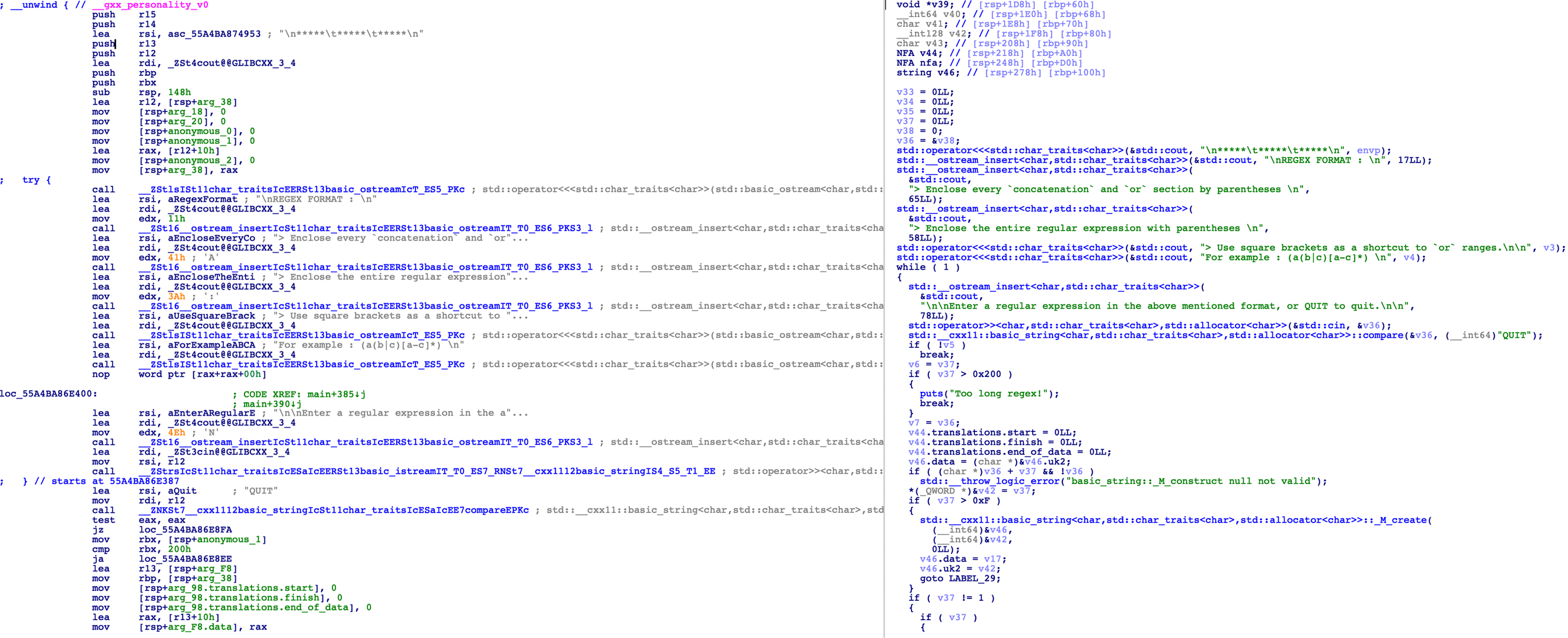
Pwnables, are challenges, where most of the time you are given a small application (e.g. a linux program) and you have to get remote code execution by finding and exploiting a vulnerability in it. Because you do not necessarily get the original source code, you have to use a disassember to extract the CPU instructions from it. With the help of a decompiler, we can turn the CPU instructions into a format, that (hopefully) resembles the original source code. (Pictured is a challenge open inside IDA, a disassembler and decompiler.)
Reversing challenges are very similar to pwnables, but the focus lies more on understanding what the program exactly does. An example is a key generator, where you have to find a valid key to make the program accept it.
As the name implies, web challenges are mostly web services that are vulnerable to some kind of attack.
Crypto - short for cryptography, mostly consists of finding weaknesses or published research for implementations of certain protocols and then exploiting those.
The last - and often most weird category - misc, focuses on all kind of different things, from scavenger hunts to steganography and more.
With this new knowledge, I finally got my hand on trying to hack a simple application. The first challenge was getting the application to run, all while the “Baby” in the name was mocking me. With some help, I got the application running and I immediately found a way to crash it (which is good). Hurray! Following some more trial and error, I triumphiantly got my first exploit working. I was hooked and started solving more and more old challenges, excitedly waiting for the next CTF event.
Can you even cat?⌗
My first CTF was the TUCTF, an online CTF, meaning anyone could participate from anywhere. As always, we met in our CTF room (CAB H52) and started hacking. The CTF had already started a day prior, which meant we had to catch up with teams that started earlier. Most of the binary challenges were quickly pwned, leaving us with the two most dreaded categories: misc and web.
The two remaining misc challenges were both related to DOS (Microsoft Disk Operating System) which made them super annoying to solve: They where both text based adventure and you had to solve some kind of puzzle to get the flag. After a lot of trial and error we managed to find the flag for the - supposedly - harder one by just sending random unix commands. We then broke it by sending a Ctrl-C (an interrupt signal) and got python execution.
Back to the ’easier’ one, where we got the following hint: what do witches usually have? Because witches usually have cats, we tried all possible variations of cat flag (which on linux prints the file flag). At the end, it turned out to be cat flag.txt. How I hate random blackbox challenges.
We quickly solved all the remaining web challenges but one (which also turned out to be a random blackbox challenge).
Nonetheless, it was a lot of fun and, even though we started a day late, we came in on place 37 out of 764.
3 bytes and even less hours of sleep⌗
The next CTF was Insomni’hack in Geneva, where we had to travel to. Up until this year, the CTF committee did not have a travel budget, as we usually can play online. So our journey began with requesting for a travel budget at the VIS general assembly.
So we travelled to Geneva, did some sight seeing and then went to the contention center, where the CTF was held. The CTF was played over night, from 18:00 to 04:00, so we brought tons of caffeinated drinks to keep us awake.
During the CTF, I tried to sole the challenge called ‘3bytes’. Opening the 3bytes binary with my favourite decompiler, it turned out to not contain much code. True to its name, the binary allowed you to write three arbitrary bytes wherever you chose. It even helpfully included the location of the libc as well as a docker container for the challenge. However, everything was randomized, so we couldn’t overwrite - for example - exit with something we control. We were pretty clueless and came back constantly during the CTF trying new approaches, stepping through everything in the libc and researching similar challenges, but we found nothing. That is until the very end of the CTF, when Yves managed to find a similar challenge that was 6 months old. But it was too late, since modifying the exploit was not trivial and would take a lot of time. Still I had a lot of fun and I tried solving some web challenges as well. Meanwhile our other teammates managed to solve one challenge by just sending random shell command. Furthermore, we managed to be the first team to solve the exploit quest challenge, a fun scavenger hunt around the convention center.

In the end, we beat all other schools that were participating (including the EPFL team ;)) and placed 9th. (Pictured is the exhausted flagbot team at the award ceremony at 4am) Given that some of the best teams around the world were participating, we were pretty satisfied with that outcome. Even more so, when we received our prizes for being the best school team. However, all of it came in a big cheap carton box with no carrying handles. Since we were close to the airport, we borrowed a luggage cart and used that to carry it around (pictured Jonas exhausted after 10 hours of CTF and now having to carry a big carton box). Of course not everything was perfect, our train back (at 5 am) was cancelled and we had to wait even longer to be able to finally try to get some sleep.

Russia still uses Windows XP?⌗
After coming home from Geneva and finally getting some sleep, I was sure of one thing: I needed more practice. While solving challenges of old CTFs is always a good exercise, participating in more CTFs would help even more, especially with time management, something often underrated for CTFs.
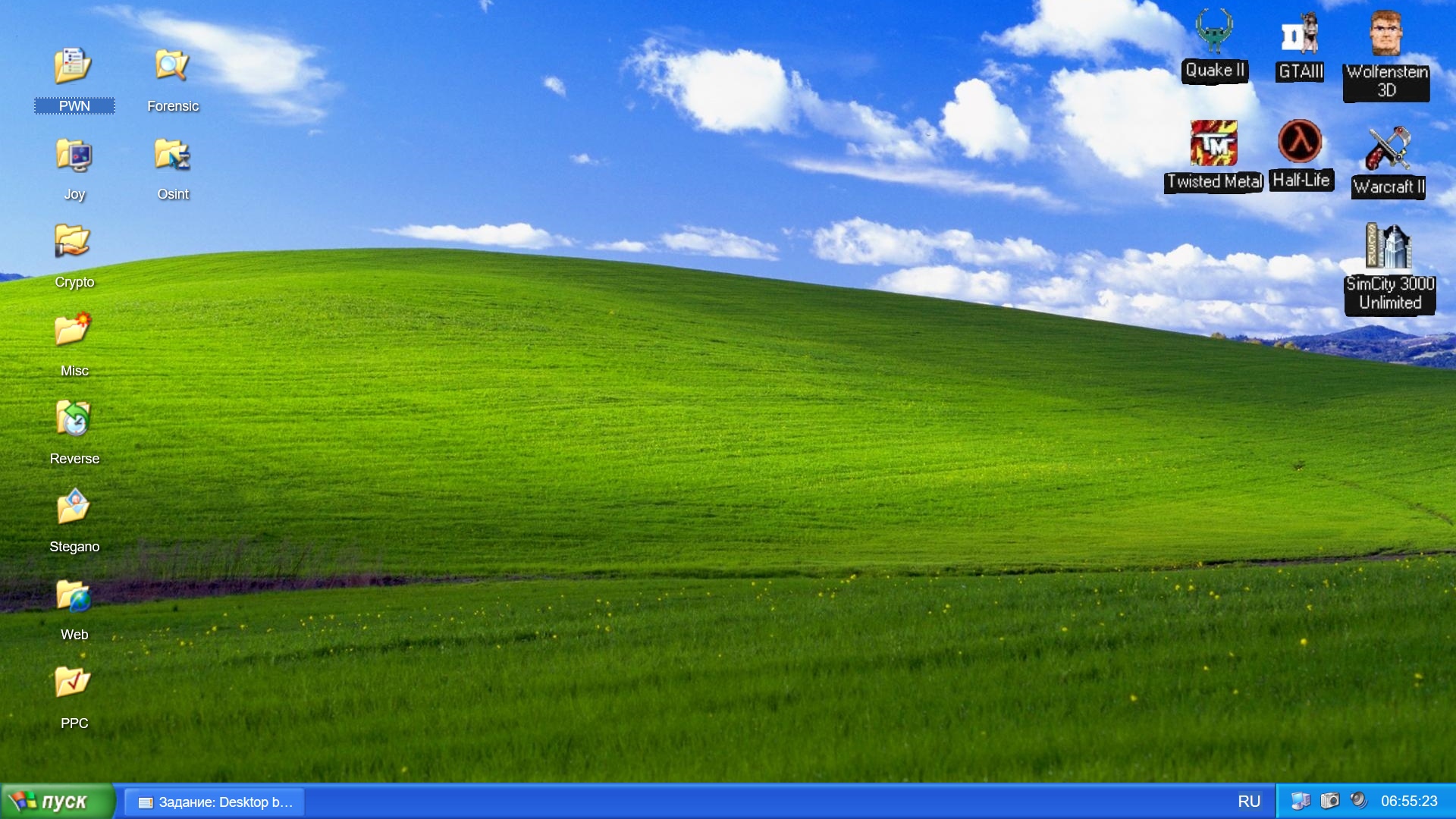
So we started by participating in a Russian CTF called TyumenCTF. Even though we were warned by the registration, that the CTF would be Windows XP themed, I was not prepared for their website: a completely normal - besides the weird folders - looking XP desktop. Luckily for us though, the challenges were still all windows based and most pwnables even came with source! Although I worked remotely, I was still able to solve some challenges and help our team secure the 6th place.
Lots of MOVs and a first place⌗
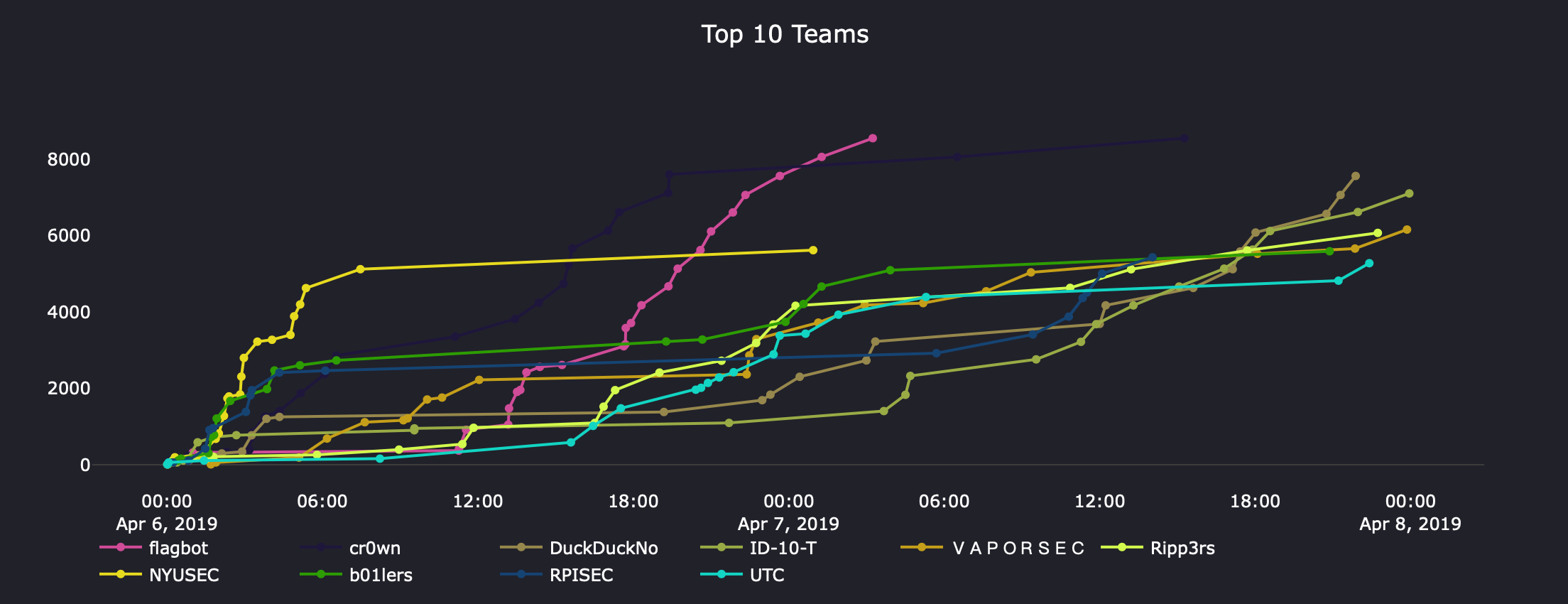
Between TyumenCTF and other events we also participated in SwampCTF. We didn’t really start solving challenges after a good few hours past the start and hence had a lot of catching up to do. But once we tasted flags, we powered through a lot of the challenges.
An interesting challenge was called “future fun”.
It was a 10Mb binary that needed some input and was tagged as reversing.
I opened it in IDA, not expecting much and was greeted by a very long loading time.
Once IDA had finally loaded the binary, it complained a lot about missing stuff.
I looked closely at the disassembly and only saw MOV instructions.
At that point I gave up, but my teammates mentioned a compiler called movfuscator: A compiler that outputs only MOV instructions, as MOV is Touring complete.
Things started to slow down though (pictured), when we completed almost all challenges. It was also getting late, so most of us decided to go home and try our luck the next day. But then suddenly we only had one challenge left and - even though we were first place now - I knew we had to try to solve it as fast as possible. We worked hard and eventually - at 3 AM - we got the final flag of the CTF and won!
This was an amazing experience and would not have been possible without my incredible teammates. I learned a lot during this CTF and I hope we will win again next year :)
Stealing exploits is fun, COBOL is not…⌗
To end the year on a high note we participated in the FaustCTF, an attack and defense CTF: Every team gets a server with vulnerable applications. The goal is to patch your own server, while simultaneously exploiting the applications running on the servers of all the other teams. This time, researching beforehand payed off immensely. We found a tool named flower, that can ingest network traffic dumps and not only filter out traffic stealing our flags, but also create exploit scripts we can use from that traffic.
Backing up a bit, we arrived at CAB and eagerly awaited the download and decryption of our VM so we can start exploiting and patching.
We hosted our sever on Google cloud and the first complication was getting the application code onto our local machines.
After that hurdle was overcome, we could finally start finding exploits.
A harmless looking web service named punchy caught my eye.
It was written in Python, but also contained native libraries that were called.
Upon opening the native libraries in IDA, I was confused.
It seemed like the native libraries were writing code to a file, then calling COBOL to compile said file and then executing the compiled binary.
I feared I would have to learn COBOL to be able to make an exploit.
But after looking at the web interface, it turned out it was even worse:
The only thing one could do, was upload punch cards with COBOL code that was then processed by the service and converted to code.
I still had hope that there was another exploit somewhere, but when checking flower for what traffic the game server sent (to store the flag), it was clear I had to somehow write COBOL code onto punch cards.
While I struggled with punchy, we were already under attack on a different service.
Although we already knew how to pwn it, our exploit was somehow failing.
Thanks to flower however, we were able to just copy the exploit that exploited us and use it as our own.
This pattern was visible throughout the whole CTF.
Once other people got their punch cards to work, I gave up and just used flower to copy their images.
We even managed to copy an exploit, for which we still have no idea how it works.
Even better, one of our applications - which nobody took a look at - was getting exploited.
But somehow we were gaining points for that service, instead of loosing them?
Turns out, one team decided to have some fun and started exploiting that service on all teams servers.
Instead of using the exploit normally, they submitted flags for other teams, meaning we were gaining points instead.
Two hours before the CTF was over, we noticed some suspicious sh sessions (a shell).
To combat attackers, [redacted] decided to kill all sh sessions.
However, not only did he run that in the host on Google cloud (instead of the VM being attacked), he also ran it in a loop.
Immediately all of us were kicked out and we had to hard reset the server.
Nevertheless, we still managed to secure a good place.
All in all, while it was a very hectic CTF, I had a lot of fun and flower was unbeatable.
We want you for flagbot!⌗
If any of this sounded interesting to you, we are always looking for new members. We have meetings on Monday from 19:00 at CAB H52 and everyone is welcome. Just drop by and someone will help you get started.

